Master’s Degree in Maritime Cybersecurity
Why this master’s programme?
The Master’s in Maritime Cybersecurity
Provides the tools and specialized knowledge to protect critical maritime infrastructure and operations against growing cyber threats. Learn to identify vulnerabilities, implement defense-in-depth strategies, and respond effectively to security incidents in the global maritime environment. This program covers everything from the protection of ICS/OT systems on board ships to the security of ports and offshore facilities, including compliance with international regulations and analysis of the latest trends in maritime cyberattacks.
Key Advantages
- Practical Approach: Attack simulations and incident response exercises in real maritime environments.
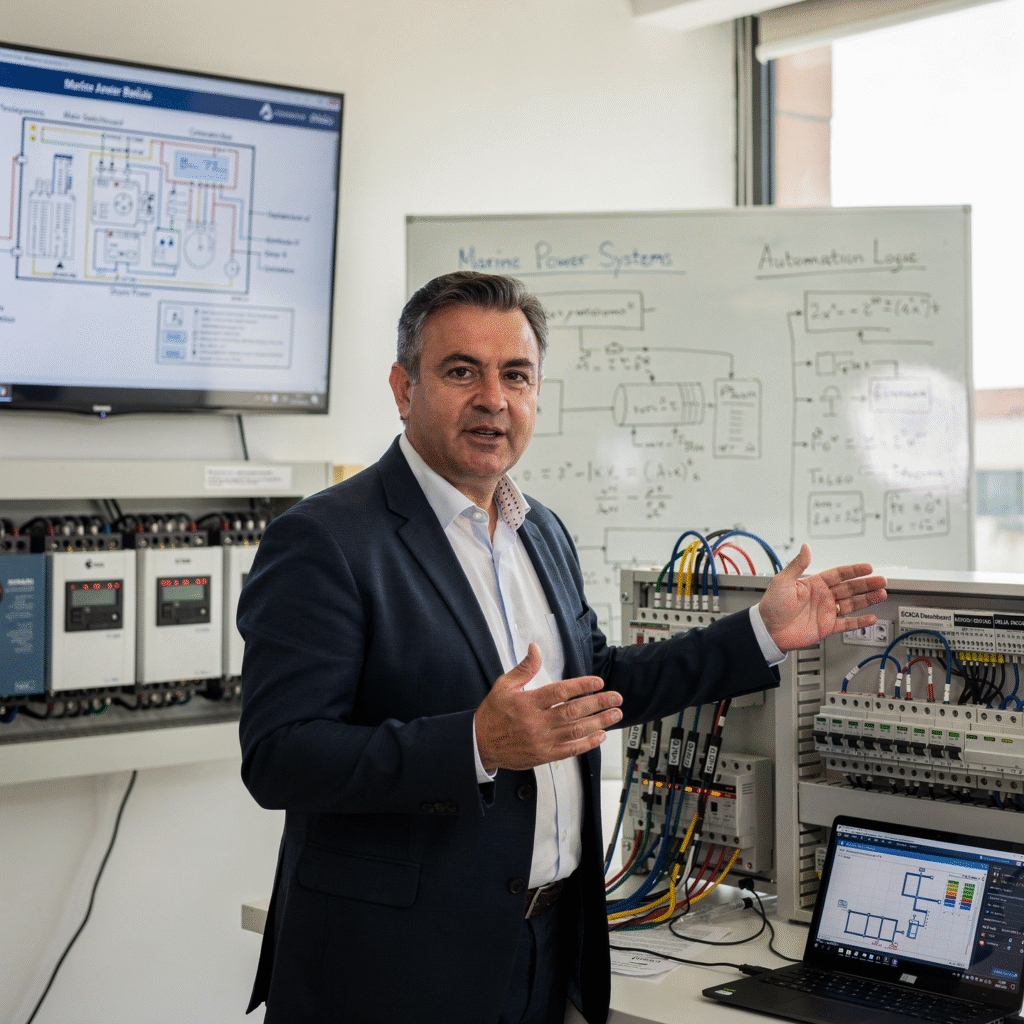
- Industry Experts: Instructors with extensive experience in maritime and naval cybersecurity.
- Comprehensive Coverage: From supply chain security to cloud data protection.
- Relevant Certifications: Preparation for key cybersecurity certifications.
- Professional Networking: Opportunities to connect with other professionals in the sector and expand your network.

- Modality: Online
- Level: Masters
- Hours: 1600 H
- Start date:
Availability: 1 in stock
Who is it aimed at?
- Information security professionals seeking to specialize in the protection of critical maritime infrastructure.
- Naval and marine engineers interested in understanding and mitigating cyber threats to ships and port systems.
- Merchant marine officers and shore-based personnel responsible for the safety of navigation and maritime operations.
- IT managers and executives in shipping and port companies who wish to implement effective cybersecurity strategies.
- Auditors and consultants seeking to develop expertise in risk assessment and regulatory compliance in maritime cybersecurity.
Flexibility and Practical Approach
Combines theory and practice with real-world case studies, simulations, and access to experts in Maritime cybersecurity for immediate application of knowledge.

Objectives and skills

Protecting critical maritime infrastructure:
“Conduct comprehensive Security Risk Assessments (SRAs), implement physical and cyber protection measures, and coordinate with port and shipping authorities for an effective response to threats.”

Managing cybersecurity incidents in maritime environments:
“Identify, classify, and respond to incidents (malware, phishing, intrusions) following the response plan and reporting to the competent authority (ISM/OCIMF).”

Assess and mitigate specific cyber risks in the maritime sector:
Implement network segmentation and hardening of critical systems (ICS/OT), continuously monitoring vulnerabilities and applying specific security patches for maritime equipment.

Design and implement resilient security architectures for ships and port facilities:
Implement network segmentation with least privilege policies and intrusion detection systems, managing incidents with predefined response plans adaptable to the evolution of threats.
Comply with national and international regulations on maritime cybersecurity:
Implement and maintain an Information Security Management System (ISMS) in accordance with ISO 27001/IMO standards, adapted to the ship and its critical systems.
Leading the response to maritime cyber crises and ensuring operational continuity:
“Implement contingency and recovery plans in the event of incidents, prioritizing crew safety, environmental protection, and effective communication with port authorities and response teams.”
Study plan – Modules
- Identification and classification of critical maritime infrastructure: ports, offshore platforms, cargo terminals, and maritime navigation systems
- Advanced cyber threat models in the maritime environment: ransomware, distributed denial-of-service (DDoS) attacks, SCADA system manipulation, and digital sabotage
- Network architectures and critical devices: analysis of ICS/SCADA systems, OT (Operational Technology) networks, and integration with IT (Information Technology)
- Cyber risk assessment methodologies specific to maritime infrastructure, including NIST and ISO/IEC 27001 frameworks adapted to maritime environments
- Design and implementation of defense-in-depth strategies: network segmentation, industrial firewalls, intrusion detection and prevention systems (IDS/IPS)
- Secure maritime communication protocols: analysis and protection of protocols such as AIS, ECDIS, VTS, and Port Automation Systems and Vulnerabilities
Advanced tools for monitoring and responding to cyber incidents in maritime infrastructure, including digital forensics and rapid response techniques for security breaches
Planning and development of resilience and business continuity plans for critical maritime systems, ensuring the availability and security of essential processes in the face of cyberattacks
International regulations and standards applicable to the cybersecurity of maritime infrastructure: ISPS, IMO MSC-FAL, and European Maritime Safety Agency (EMSA) guidelines
Training and awareness-raising for operational and security personnel in maritime cybersecurity: best practices, drills, and managing the human factor as a key element in comprehensive protection
- Fundamentals of Industrial Control Systems (ICS) in maritime environments: structure, components, and essential functions
- Evaluation of classic and modern architectures for SCADA and DCS systems on maritime platforms
- ISA/IEC 62443 reference models applied to security in maritime industrial control systems
- Implementation of network segmentation: zones, conduits, and security perimeters in onboard facilities and port terminals
- Secure industrial protocols: Modbus TCP/IP, DNP3, OPC UA, and Profinet with a focus on encryption and authentication strategies
- Design and deployment of firewalls specifically for ICS and maritime systems: policies, rules, and prevention of unauthorized access
- Methodologies for detecting and responding to cyber incidents in maritime SCADA systems: real-time monitoring techniques and digital forensics
- Integration of IDS/IPS solutions adapted to industrial protocols and maritime networks: signatures, anomalies, and machine learning
- Hardening and access control on ICS devices: patch management, multi-factor authentication, and application whitelisting
- International regulations and standards related to maritime industrial cybersecurity: IMO, IEC 62443, and NIST compliance
- Risk assessment and technical audits of maritime control systems: vulnerability identification and mitigation plans
- Business continuity and disaster recovery plans (DRPs) for critical maritime infrastructure
- Real-world case studies of cyberattacks on maritime industrial systems and advanced defense strategies
- Use of emerging technologies: artificial intelligence, blockchain, and quantum cryptography for the protection of maritime control systems
- Training in secure communication protocols for ICS operators and security teams in the Maritime sector
Advanced simulation and practice in laboratory environments with maritime SCADA systems to consolidate technical skills
- Comprehensive cybersecurity risk assessment in port infrastructure: identification, categorization, and prioritization of specific threats to the maritime industrial environment
- Industrial OT network architectures in ports: design, segmentation, and implementation of secure zones for the protection of SCADA and PLC systems against advanced attacks
- Industrial communication protocols (Modbus, DNP3, OPC-UA): inherent vulnerabilities and advanced techniques for their monitoring and strengthening in marine environments
- Integration and deployment of SIEM and SOAR solutions in port environments for proactive detection, analysis, and automated response to critical cyber incidents
- Application of artificial intelligence and machine learning techniques for the identification of anomalous patterns in operational data and the prevention of intrusions into maritime control systems
- Implementation of robust access controls and identity management in industrial systems, including the use of Multi-factor authentication and least privilege policies
Development of response and recovery plans for specialized cyber incidents in ports, considering operational continuity and mitigation of cascading impacts
Applicable international regulations and standards (NIST, IEC 62443, IMO guidelines): compliance, audits, and continuous improvement in maritime cybersecurity
Penetration testing and vulnerability assessments specific to port infrastructure: methodologies, tools, and professional reporting of findings
Advanced training and awareness for port operators and technical personnel, focused on the prevention, detection, and management of complex cyber incidents
- Fundamentals of Cyber Intelligence in Maritime Environments: Definition, Objectives, Intelligence Sources, and Intelligence Cycle Applied to Critical Port Infrastructure
- OT/IT and SCADA Architectures in Maritime Systems: Topologies, Industrial Protocols (Modbus, DNP3, OPC UA), Integration, and Specific Attack Vectors
- Advanced Penetration Testing Techniques in Maritime OT and IT Environments: Reconnaissance, Scanning, Exploitation, and Post-Exploitation in Naval and Port Industrial Networks
- Simulation Methodologies and Red/Blue Team Exercises on Ship and Port Simulator Platforms: Organization, Roles, Masking, and Results Analysis
- Digital Forensic Investigation in Maritime Cyberattacks: Evidence Acquisition, Log and Artifact Analysis, Data Recovery, and Chain of Custody in Environments with SCADA Systems
- Mitigation of GNSS Spoofing Attacks and AIS: Identification of spoofing techniques, technical countermeasures such as cryptographic authentication, advanced filters, and continuous monitoring
Incident response and containment in maritime environments: Creation of specific OT/IT playbooks, interdepartmental coordination, and effective communication with maritime authorities
Implementation of cybersecurity solutions based on artificial intelligence and machine learning for the proactive detection of intrusions and anomalies in maritime systems
Applicable international regulations and standards: In-depth analysis of IMO Guidelines, NIST SP 800-82, IEC 62443, and their practical application in maritime infrastructure security
Advanced methodologies for the evaluation and continuous improvement of cyber resilience in ports and maritime fleets, integrating audits, drills, and technical reviews
- OT/IT Network Architecture and Topologies in Maritime Environments: Differentiation, Convergence, and Advanced Segmentation
- Digital Forensics Applied to Maritime Systems: Evidence Recovery in Industrial and Shipping Environments
- Specific Threat Models for Critical Maritime Infrastructure: Attack Vectors, Common Vulnerabilities, and Risk Scenarios
- Implementation of Proactive Intrusion Detection Methodologies: IDS/IPS Systems Specialized in Maritime and OT Protocols
- Risk Assessment and Mitigation in SCADA and PLC Technologies Present in Smart Platforms and Vessels
- International Frameworks and Regulations Applicable to Maritime OT/IT Cybersecurity: NIST, IEC 62443, IMO, and Their Integration into Corporate Policies
- Application of Artificial Intelligence and Machine Learning for Continuous Monitoring and Predictive Threat Analysis in Combined Networks
- Advanced segmentation and microsegmentation techniques to protect the integrity and availability of critical maritime systems
- Cyber incident management in maritime environments: response plans, effective communication, and rapid operational recovery
- Simulations and practical exercises of targeted attacks (APTs) on maritime networks to strengthen organizational resilience
- Design of defense-in-depth architectures for integrated OT/IT systems: firewalls, secure gateways, and role-based access controls
- Secure communication protocols and encryption in maritime networks: effective implementation in legacy and modern protocols
- Real-time monitoring and analysis of network traffic and logs to identify anomalies and attack patterns in maritime systems
- Integration of SIEM and SOAR solutions specifically for maritime environments: automation in threat detection and response
- Impact of cyber threats on Physical and operational security of maritime assets: interdependent risk analysis
Audits and penetration tests of maritime OT/IT infrastructures: advanced methodologies and tools
Specialized training and awareness for operational and technical personnel in proactive defense against cyberattacks
Development of cyber intelligence strategies to anticipate attack campaigns targeting the maritime industry
Evaluation of the ecosystem of technology providers and partners in terms of risks and compliance with OT/IT cybersecurity standards
Study of real-world cases of cyber incidents in the maritime sector and critical analysis of the defense strategies applied
- Fundamentals of OT/IT networks in maritime environments: topologies, specific protocols, and technological convergence
- Advanced threat analysis methodologies: threat intelligence, proactive hunting, and behavior-based detection
- Identification and classification of attack vectors in maritime systems: SCADA, PLCs, IoT sensors, and satellite communications
- Tools and techniques for continuous monitoring and forensic analysis in integrated maritime networks
- Implementation of defense-in-depth systems for OT/IT environments: segmentation, micro-segmentation, and granular access control
- Security protocols for maritime communications: encryption, authentication, and certificate management in industrial networks
- Assessment of specific vulnerabilities: firmware analysis, exploitation of vulnerabilities in navigation and maritime automation systems
- Development and integration of cybersecurity policies adapted to the maritime operational context and
- Current international regulations
- Simulation of attack and response scenarios: red teaming and purple teaming techniques adapted to maritime OT/IT environments
- Planning and execution of proactive actions: updates, patches, targeted hardening, and crew cybersecurity training
- Comprehensive incident management: early detection, containment, eradication, and recovery in combined maritime OT/IT systems
- Application of artificial intelligence and machine learning for advanced detection of anomalies and persistent threats in maritime networks
- Integration of SIEM and SOAR systems into maritime infrastructure to automate incident response and improve operational resilience
- International regulations and standards applicable to maritime cybersecurity: IMO, IEC 62443, NIST, and their practical implementation
- Real-world case studies and analysis of global cyberattacks in the maritime industry: lessons learned
Lessons learned and technological improvements
Governance and control frameworks for the continuous management of cyber risks in integrated maritime OT/IT networks
Design and execution of specific cybersecurity audits for critical maritime infrastructures
Emerging trends in maritime cybersecurity: future threats, disruptive technologies, and adaptive defense strategies
- Identification and classification of critical maritime infrastructure: ports, shipyards, offshore platforms, and navigation systems
- Analysis of advanced cyber threats: APTs (Advanced Persistent Threats), ransomware, DDoS attacks, and specific vectors in marine environments
- International regulatory framework and applicable regulations in maritime cybersecurity: IMO, NIST, ISA/IEC 62443, and EU guidelines
- Design and implementation of cybersecurity policies for critical maritime infrastructure, including network segmentation and role-based access control (RBAC)
- Defense-in-depth architectures for maritime environments: industrial firewalls, maritime IDS/IPS, and AI-based anomaly detection systems
- Secure communication and authentication protocols in maritime SCADA and OT (Operational Technology) systems
- Monitoring and Incident response: Integration of marine SIEM with industry-specific threat intelligence tools
Digital forensics in maritime environments: Techniques for evidence preservation, attack reconstruction, and malicious actor tracking
Cyberattack simulation and exercises for resilience testing and continuous improvement of incident response plans
Inter-agency coordination and contingency plans for rapid recovery of critical operations post-cyberattack
- Fundamentals of industrial networks in maritime environments: topologies, specific protocols (MODBUS, PROFIBUS, EtherNet/IP), and operational characteristics
- Secure network design for Industrial Control Systems (ICS): segmentation, demilitarized zones (DMZs), and applicability on offshore platforms and vessels
- Integration of OT (Operational Technology) networks with IT: interoperability challenges and risks in maritime industrial cybersecurity
- Integrated maritime communication protocols: NMEA 0183, NMEA 2000, and their protection against cyberattacks
- Implementation of industrial firewalls and intrusion prevention systems (IDS/IPS) in critical maritime networks
- Security in satellite and radio frequency communications: encryption, authentication, and interference mitigation in maritime environments
- Advanced management of vulnerabilities and persistent threats in marine ICS environments: case studies and proactive methodologies
- Automation and continuous monitoring of secure networks: use of SCADA and SIEM systems adapted to maritime infrastructures
- Implementation of access policies, user control, and identity management in critical maritime systems
- International regulations and standards applicable to cybersecurity in maritime industrial control networks (IEC 62443, NIST, IMO guidelines)
- Incident response and disaster recovery plans in integrated maritime networks: procedures, simulations, and continuous improvement
- Technical audits and certification of secure network infrastructures in the maritime sector: tools and best practices
- Case studies of attacks and vulnerabilities exploited in maritime ICS networks: analysis, mitigation, and lessons learned
- Emerging trends in cybersecurity for Integrated maritime communications: 5G networks, industrial IoT, and blockchain applied to security
Capacity to design, implement, and manage robust, secure networks that guarantee comprehensive protection of Industrial Control Systems and maritime communications against advanced threats
- Fundamentals and architecture of critical maritime infrastructure: types, components, and inherent vulnerabilities
- Advanced cyber threat models applied to industrial control systems (ICS) in maritime environments: attack vectors and intrusion techniques
- Security in SCADA and DCS systems: protocols, authentication, network segmentation, and isolation of critical systems
- Implementation of defense-in-depth strategies: industrial firewalls, IDS/IPS systems specific to maritime environments, and role-based access control
- Cryptography applied to maritime communications and industrial control systems: algorithms, key management, and real-time encryption
- Anomaly detection and early response using machine learning techniques and behavior analytics applied to sensor and network data
- Integration of OT and IT systems: interoperability challenges, unified risk management, and secure architectures Hybrid systems
- Maritime cybersecurity management and governance policies: international standards, specific regulations (IMO, IEC 62443, NIST), and best practices
- Planning and execution of cyber simulation exercises (red team/blue team) for critical maritime infrastructure: design, metrics, and continuous improvement
- Operational continuity and incident recovery: contingency plans, backups, and resilience strategies against cyberattacks in ICS systems
- Definition and characterization of critical maritime infrastructure: ports, terminals, shipyards, and logistics hubs
- Advanced cybersecurity risk assessment: advanced persistent threats (APTs), attack vectors, and analysis of vulnerabilities specific to the maritime environment
- International regulatory framework and cybersecurity regulations applied to critical maritime infrastructure (IMO, NIST, IEC 62443)
- Design and application of integrated resilience strategies: redundancy, network segmentation, and defense-in-depth architectures
- Implementation of cyber defense technologies: intrusion detection and response systems (IDS/IPS), next-generation firewalls, and anomalous behavior analysis using AI
- Planning and execution of cybersecurity drills and exercises in simulated and real maritime environments
- Integration of industrial control systems (ICS/SCADA) with Secure protocols and robust authentication mechanisms
Cyber incident management policies: from detection, containment, and eradication to operational recovery and digital forensics
Development of business continuity and disaster recovery plans for critical maritime systems
Assessment and mitigation of risks associated with IoT and IIoT interconnectivity in the maritime logistics and operational chain
Application of maritime cyber intelligence for anticipating and neutralizing strategic cyberattacks
Roles and responsibilities in maritime cybersecurity governance: response team, coordination with government agencies and private operators
Ethical and legal aspects of cybersecurity management applied to the maritime sector
Development and presentation of the final integrative project: proposal of a comprehensive resilience and cyber defense strategy for a specific critical maritime infrastructure, with detailed technical analysis and roadmaps for its implementation implementation
Career prospects
“`html
- Maritime Cybersecurity Analyst: Protection of systems and networks on board and ashore.
- Maritime Cybersecurity Consultant: Advising companies on security risks and solutions.
- Ship Security Officer (SSO): Implementation of security measures and response to cyber incidents.
- Maritime Cyber Risk Manager: Identification and assessment of risks to maritime security.
- Maritime Cybersecurity Auditor: Evaluation of compliance with security standards and regulations.
- Maritime Cyber Incident Investigator: Forensic analysis of incidents to determine causes and responsibilities.
- Secure Software Developer for the Sector Maritime: Creating applications and systems resistant to cyberattacks.
Port and Coastal Facility Cybersecurity Specialist: Protecting critical port infrastructure.
“`



Entry requirements

Academic/professional profile:
Bachelor’s degree in Nautical Science/Maritime Transport, Naval/Marine Engineering or a related qualification; or proven professional experience on the bridge/in operations.

Language proficiency:
Functional Maritime English (SMCP) recommended for simulations and technical materials.

Documentation:
Updated CV, copy of qualification or seaman’s book, national ID/passport, motivation letter.
Technical requirements (for online):
Device with camera/microphone, stable internet connection, monitor ≥ 24” recommended for ECDIS/Radar-ARPA.
Admissions process and dates

Online
application
(form + documents).

Academic review and interview
Admissions decision

Admissions decision
(+ scholarship offer if applicable).
Place reservation
(deposit) and enrolment.

Induction
(access to the virtual campus, calendars, simulator guides).
Scholarships and financial support
- Proactive Defense: Learn to anticipate and neutralize cyberattacks specific to the maritime sector.
- Regulations and Compliance: Master security standards (IMO, ISO 27001) and avoid penalties.
- Real-Time Simulations: Test your skills in controlled environments that replicate real-world scenarios.
- Expert Team: Train with leading professionals in cybersecurity and maritime law.
- Comprehensive Protection: Ensure the operational continuity of ships, ports, and critical infrastructure.

Testimonials
This Master’s degree in Maritime Cybersecurity provided me with the tools and knowledge necessary to identify and mitigate vulnerabilities in naval systems. After completing it, I secured a position as a Security Analyst at a major shipping company, where I successfully implemented a new intrusion detection system that has significantly improved the security of our fleet.

I applied my master’s degree knowledge to the coordination of a multinational maritime security exercise, achieving unprecedented interoperability among the participating forces and successfully neutralizing simulated threats. This resulted in recognition from the Admiralty and an invitation to join the naval defense strategic planning team.

“The Master’s in Maritime Cybersecurity provided me with the tools and specialized knowledge to lead the implementation of a new security system in our fleet. Thanks to the training received, we were able to reduce security incidents related to intrusions into navigation and control systems by 80%, optimizing the protection of sensitive data and operational efficiency.”

After completing the Master’s in Maritime Cybersecurity, I secured a position as a Senior Security Analyst at a major shipping company. I applied the knowledge gained in the Master’s program to develop and implement a new intrusion detection system for the fleet, reducing cybersecurity incidents by 60% in the first year. This resulted in significant cost savings for the company and a considerable increase in the security of maritime operations.

Frequently asked questions
Maritime sector.
Yes. The itinerary includes ECDIS/Radar-ARPA/BRM with harbor, ocean, fog, storm, and SAR scenarios.
Online with live sessions; hybrid option for simulator/practical placements through agreements.
Maritime industry.
Recommended functional SMCP. We offer support materials for standard phraseology.
Yes, with a relevant degree or experience in maritime/port operations. The admissions interview will confirm suitability.
Optional (3–6 months) through Companies & Collaborations and the Alumni Network.
Simulator practice (rubrics), defeat plans, SOPs, checklists, micro-tests and applied TFM.
A degree from Navalis Magna University + operational portfolio (tracks, SOPs, reports and KPIs) useful for audits and employment.
- Definition and characterization of critical maritime infrastructure: ports, terminals, shipyards, and logistics hubs
- Advanced cybersecurity risk assessment: advanced persistent threats (APTs), attack vectors, and analysis of vulnerabilities specific to the maritime environment
- International regulatory framework and cybersecurity regulations applied to critical maritime infrastructure (IMO, NIST, IEC 62443)
- Design and application of integrated resilience strategies: redundancy, network segmentation, and defense-in-depth architectures
- Implementation of cyber defense technologies: intrusion detection and response systems (IDS/IPS), next-generation firewalls, and anomalous behavior analysis using AI
- Planning and execution of cybersecurity drills and exercises in simulated and real maritime environments
- Integration of industrial control systems (ICS/SCADA) with Secure protocols and robust authentication mechanisms
Cyber incident management policies: from detection, containment, and eradication to operational recovery and digital forensics
Development of business continuity and disaster recovery plans for critical maritime systems
Assessment and mitigation of risks associated with IoT and IIoT interconnectivity in the maritime logistics and operational chain
Application of maritime cyber intelligence for anticipating and neutralizing strategic cyberattacks
Roles and responsibilities in maritime cybersecurity governance: response team, coordination with government agencies and private operators
Ethical and legal aspects of cybersecurity management applied to the maritime sector
Development and presentation of the final integrative project: proposal of a comprehensive resilience and cyber defense strategy for a specific critical maritime infrastructure, with detailed technical analysis and roadmaps for its implementation implementation
Request information
Complete the Application Form.
Attach your CV/degree certificate (if you have it to hand).
Indicate your preferred cohort (January/May/September) and whether you would like the hybrid option with simulator sessions.
An academic advisor will contact you within 24–48 hours to guide you through the admission process, scholarships, and compatibility with your professional schedule.
Faculty

Eng. Tomás Riera
Full Professor
Eng. Tomás Riera
Full Professor

Eng. Sofía Marquina
Full Professor
Eng. Sofía Marquina
Full Professor
Eng. Javier Bañuls
Full Professor
Eng. Javier Bañuls
Full Professor

Dr. Nuria Llobregat
Full Professor
Dr. Nuria Llobregat
Full Professor

Dr. Pau Ferrer
Full Professor
Dr. Pau Ferrer
Full Professor

Cap. Javier Abaroa (MCA)
Full Professor
Cap. Javier Abaroa (MCA)
Full Professor
