Diploma in Digital Emergency Protocols
Why this certificate program?
The Diploma in Digital Emergency Protocols
This program prepares you to lead the response to cyber incidents, from detection to recovery. Learn to mitigate the impact of attacks, protect critical information, and ensure business continuity. It provides you with the tools and knowledge necessary to implement effective response plans, complying with security regulations and minimizing risks. Master the techniques of digital forensics, crisis management, and strategic communication in emergency situations.
Differentiating Advantages
- Practical Simulations: Participate in realistic cyberattack scenarios to develop response skills.
- Cutting-Edge Tools: Learn to use specialized software for incident detection, analysis, and containment.
- Expert Mentors: Receive personalized guidance from professionals with extensive experience in cybersecurity.
- Professional Certification: Obtain a recognized diploma that validates your skills in digital emergency management.
- Strategic Networking: Connect with other professionals in the sector and expand your network.

- Modality: Online
- Level: Diplomado
- Hours: 800 H
- Start date: 13-06-2026
Availability: 1 in stock
Who is it aimed at?
- Digital marketing and communications professionals seeking to master online crisis management, network monitoring, and incident response.
- Cybersecurity and information security managers needing to delve deeper into breather response protocols, digital forensics, and reputation management.
- Public relations and corporate communications teams requiring effective contingency plans, critical scenario simulations, and uncertainty management tools.
- Executives and managers from companies across all sectors interested in protecting their brand image, minimizing reputational damage, and strengthening stakeholder trust.
- Students and recent graduates in related fields seeking innovative specialization and enhanced skills in-demand skills and a differentiated professional profile in the job market.
Flexibility and immediate applicability:
Designed for active professionals: live online classes, practical case studies based on real-world experiences, and tools for immediate application in your daily professional life.

Objectives and competencies

Managing communication in a digital crisis:
“Implement a predefined response plan, adapting it to the specific situation and prioritizing transparency, empathy and speed in communication through the relevant digital channels.”

Coordinate the technical response to cyber incidents:
“Prioritize containment, forensic analysis, and service recovery, communicating with relevant stakeholders and escalating according to the incident response plan.”

Adapting emergency protocols to specific digital environments:
“Develop redundant and secure digital communication plans for evacuation, including alternative channels and recipient verification.”

Strengthening organizational resilience to digital emergencies:
Implement a robust business continuity plan, prioritizing the recovery of critical data and effective communication with stakeholders.
Implementing business continuity strategies in cyberspace:
Implement backup and disaster recovery solutions for cybersecurity, prioritizing critical systems and sensitive data, with regular testing and continuous updates.
Leading the recovery of systems after digital disasters:
“Prioritize the restoration of critical services, coordinate technical teams, and communicate progress to stakeholders.”
Curriculum - Modules
- Comprehensive Maritime Incident Management: protocols, roles, and chain of command for coordinated response
- Operational Planning and Execution: briefing, routes, weather windows, and go/no-go criteria
- Rapid Risk Assessment: criticality matrix, scene control, and decision-making under pressure
- Operational Communication: VHF/GMDSS, standardized reports, and inter-agency liaison
- Tactical Mobility and Safe Boarding: RHIB maneuvers, approach, mooring, and recovery
- Equipment and Technologies: PPE, signaling, satellite tracking, and field data logging
- Immediate Care of the Affected: primary assessment, hypothermia, trauma, and stabilization for evacuation
- Adverse Environmental Conditions: swell, Visibility, flows, and operational mitigation
Simulation and training: critical scenarios, use of VR/AR, and exercises with performance metrics
Documentation and continuous improvement: lessons learned, indicators (MTTA/MTTR), and SOP updates
- Introduction to Cybersecurity: Concepts, Threats, and Vulnerabilities
- Fundamentals of Digital Crisis: Types, Impact, and Scenarios
- Digital Resilience Frameworks: NIST, ISO 27001, and Best Practices
- Cyber Risk Analysis: Identification, Assessment, and Prioritization
- Business Continuity Plans (BCP) and Disaster Recovery Plans (DRP)
- Cyber Incident Response: Detection, Containment, Eradication, and Recovery
- Digital Crisis Communication: Strategies for Stakeholders and the Media
- Legal and Regulatory Aspects: Privacy, Data Protection, and Compliance
- Threat Intelligence: Sources, Analysis, and Use
- Resilience Drills and Tests: Tabletop Exercises, Penetration Testing, and Red Teams
‘
- Introduction to Cybersecurity: Basic concepts, threats, and vulnerabilities.
- Fundamentals of Digital Crisis Management: Risk identification, assessment, and prioritization.
- Legal and Regulatory Framework: Legal compliance in cybersecurity and data protection.
- Business Impact Analysis (BIA): Identification of critical assets and key processes.
- Developing a Business Continuity Plan (BCP): Recovery and restoration strategies.
- Cyber Incident Response Team (CSIRT) Plan: Detection, analysis, containment, eradication, and recovery.
- Crisis Communication: Internal and external communication strategies during a cyber incident.
- Drills and Recovery Testing: Validation and continuous improvement of business continuity and incident response plans.
Cloud Security: Risks and best practices for protecting data and applications in cloud environments.
Current Trends in Cybersecurity: Artificial intelligence, machine learning, and their application in cyber defense.
‘
- Introduction to Cybersecurity: Concepts, Threats, and Vulnerabilities
- Network Fundamentals: TCP/IP, Protocols, Network Security
- Secure Operating Systems: Hardening, Patch Management, Access Control
- Cryptography: Algorithms, Hashing, Digital Signatures, and PKI
- Malware Analysis: Types of Malware, Detection and Analysis Techniques
- Web Application Security: OWASP Top 10, Penetration Testing
- Digital Forensics Fundamentals: Evidence Collection, Preservation, and Analysis
- Digital Forensics Tools: EnCase, FTK, Autopsy
- Security Incident Management: Detection, Response, and Recovery
- Legal and Ethical Framework of Cybersecurity and digital forensics
‘
- Introduction to Cybersecurity: Basic concepts, threats, and vulnerabilities.
- DRP Fundamentals: Business Impact Analysis (BIA) and risk assessment.
- Digital Resilience: Business continuity and disaster recovery strategies.
- Identification and classification of critical assets for the organization.
- Cyber threats: Malware, phishing, ransomware, DDoS attacks, social engineering.
- Software and hardware vulnerabilities: Patch and update management.
- Security controls: Technical, administrative, and physical.
- Development of information security policies and procedures.
- Incident response plans: Detection, containment, eradication, Recovery and lessons learned.
- Legal and regulatory framework in Cybersecurity, DRP and Digital Resilience.
‘
- System Architecture and Components: Structural design, materials, and subsystems (mechanical, electrical, electronic, and fluid) with selection and assembly criteria for marine environments
- Fundamentals and Principles of Operation: Physical and engineering foundations (thermodynamics, fluid mechanics, electricity, control, and materials) that explain performance and operating limits
- Safety and Environmental (SHE): Risk analysis, PPE, LOTO, hazardous atmospheres, spill and waste management, and emergency response plans
- Applicable Regulations and Standards: IMO/ISO/IEC requirements and local regulations;
- Conformance criteria, certification, and best practices for operation and maintenance
- Inspection, testing, and diagnostics: Visual/dimensional inspection, functional testing, data analysis, and predictive techniques (vibration, thermography, fluid analysis) to identify root causes
- Preventive and predictive maintenance: Hourly/cycle/seasonal plans, lubrication, adjustments, calibrations, consumable replacement, post-service verification, and operational reliability
- Instrumentation, tools, and metrology: Measuring and testing equipment, diagnostic software, calibration and traceability; selection criteria, safe use, and storage
- Onboard integration and interfaces: Mechanical, electrical, fluid, and data compatibility; Sealing and watertightness, EMC/EMI, corrosion protection, and interoperability testing.
Quality, acceptance testing, and commissioning: process and materials control, FAT/SAT, bench and sea trials, go/no-go criteria, and evidence documentation.
Technical documentation and integrated practice: logs, checklists, reports, and a complete case study (safety → diagnosis → intervention → verification → report) applicable to any system.
- Introduction to Cybersecurity: Basic concepts and terminology.
- Identification of Critical Assets: Mapping digital infrastructure and sensitive data.
- Cybersecurity Risk Analysis: Methodologies and tools for assessing threats and vulnerabilities.
- Legal and Regulatory Framework: GDPR, NIS2, ENS and other relevant regulations.
- Common Cyber Threats: Malware, phishing, ransomware, DDoS, and supply chain attacks.
- Threat Intelligence: Information sources and predictive analytics.
- Prevention Strategies: Firewalls, IPS/IDS, WAF and endpoint security.
- Incident Detection and Response: Contingency plans and cyber crisis management.
- Cloud Cybersecurity: Data and application protection in cloud environments.
- Awareness and Training: Training programs for employees and users.
‘
Career opportunities
- Digital Crisis Manager: Leadership in cyber incident response, coordination of multidisciplinary teams.
- Emergency Cybersecurity Analyst: Detection, analysis, and containment of digital threats during critical situations.
- Digital Resilience Consultant: Design and implementation of business continuity and disaster recovery plans.
- Digital Crisis Communications Specialist: Online reputation management and effective communication with stakeholders during emergencies.
- Information Security Incident Response Coordinator: Implementation of protocols and procedures for managing digital emergencies.
- Emergency Security Auditor: Evaluation and improvement of information security in crisis situations.
- Digital Forensic Investigator: Collection and analysis of digital evidence for identifying causes and those responsible in security incidents.
- Developer of digital emergency response tools: Creation and maintenance of technological solutions for managing cyber crises.
“`



Admission requirements

Academic/professional profile:
Degree/Bachelor's degree in Nautical Science/Maritime Transport, Naval/Marine Engineering, or a related field; or proven professional experience in bridge/operations.

Language proficiency:
Recommended functional maritime English (SMCP) for simulations and technical materials.

Documentation:
Updated resume, copy of degree or seaman's book, ID card/passport, letter of motivation.
Technical requirements (for online):
Equipment with camera/microphone, stable connection, ≥ 24” monitor recommended for ECDIS/Radar-ARPA.
Admission process and dates

1. Online
application
(form + documents).

2. Academic review and interview
(profile/objectives/schedule compatibility).

3. Admission decision
(+ scholarship proposal if applicable).
4. Reservation of place
(deposit) and registration.

5. Induction
(access to campus, calendars, simulator guides).
Scholarships and grants
- Immediate Response: Master the protocols to act effectively in the face of digital crises.
- Risk Analysis: Learn to identify and mitigate critical cyber threats to your organization.
- Strategic Communication: Develop skills to manage communication in emergency situations, protecting your reputation.
- Cutting-Edge Tools: Familiarize yourself with the latest technologies and software for incident management.
- Practical Drills: Participate in realistic simulations to strengthen your reaction and decision-making capabilities.

Testimonials
The Diploma in Digital Emergency Protocols provided me with the tools and knowledge necessary to lead the response to a cybersecurity incident in my company. Thanks to the practical simulations and the focus on crisis management, I was able to implement an effective contingency plan that minimized the impact of a recent ransomware attack, recovering our critical systems in record time and preventing significant losses.

I applied the knowledge gained from the diploma program to strengthen my company’s network security, successfully mitigating a phishing attempt that could have compromised sensitive information. Thanks to the training in navigation systems, we optimized our logistics fleet’s routes, reducing fuel costs by 15% and improving delivery times.

“This diploma program provided me with the tools and knowledge necessary to effectively manage a cybersecurity crisis. I was able to apply the strategies I learned during a real incident at my company, minimizing the impact and quickly recovering our systems. Thanks to the training I received, I feel much more confident and prepared to face any digital emergency.”

This diploma program provided me with the tools and knowledge necessary to efficiently manage a digital crisis. Thanks to practical simulations and the analysis of real-world cases, I was able to develop a security incident response plan, which allowed me to contain a security breach in my company, minimizing its impact and protecting the organization’s reputation.

Frequently asked questions
Security incidents such as data breaches, malware attacks, denial of service, phishing, and account compromise, among others.
Yes. The itinerary includes ECDIS/Radar-ARPA/BRM with harbor, ocean, fog, storm, and SAR scenarios.
Online with live sessions; hybrid option for simulator/practical placements through agreements.
Cyberattacks, system failures, data loss, security breaches, natural disasters affecting digital infrastructure, disinformation campaigns, and crisis management on social media.
Recommended functional SMCP. We offer support materials for standard phraseology.
Yes, with a relevant degree or experience in maritime/port operations. The admissions interview will confirm suitability.
Optional (3–6 months) through Companies & Collaborations and the Alumni Network.
Simulator practice (rubrics), defeat plans, SOPs, checklists, micro-tests and applied TFM.
A degree from Navalis Magna University + operational portfolio (tracks, SOPs, reports and KPIs) useful for audits and employment.
- Fundamentals of Digital Resilience: Concepts, Scope, and Benefits
- Identifying Critical Assets: Data, Systems, Infrastructure, and Personnel
- Risk and Vulnerability Analysis: Threats, Impacts, and Probability
- Developing Prevention Strategies: Proactive Cybersecurity, Hardening, and Segmentation
- Incident Response Plan: Detection, Containment, Eradication, and Recovery
- Crisis Communication: Strategies for Internal and External Stakeholders
- Business Continuity Plan: Recovery of Essential Functions
- Testing and Drills: Plan Validation, Gap Identification, and Continuous Improvement
- Recovery from Disasters: Backup, Replication, and Restoration Strategies
Regulatory and Legal Compliance: Data Privacy, Critical Infrastructure Protection
‘
Request information
Complete the Application Form.
Attach your CV/degree certificate (if you have it to hand).
Indicate your preferred cohort (January/May/September) and whether you would like the hybrid option with simulator sessions.
An academic advisor will contact you within 24–48 hours to guide you through the admission process, scholarships, and compatibility with your professional schedule.
Faculty

Eng. Tomás Riera
Full Professor
Eng. Tomás Riera
Full Professor

Eng. Sofía Marquina
Full Professor
Eng. Sofía Marquina
Full Professor
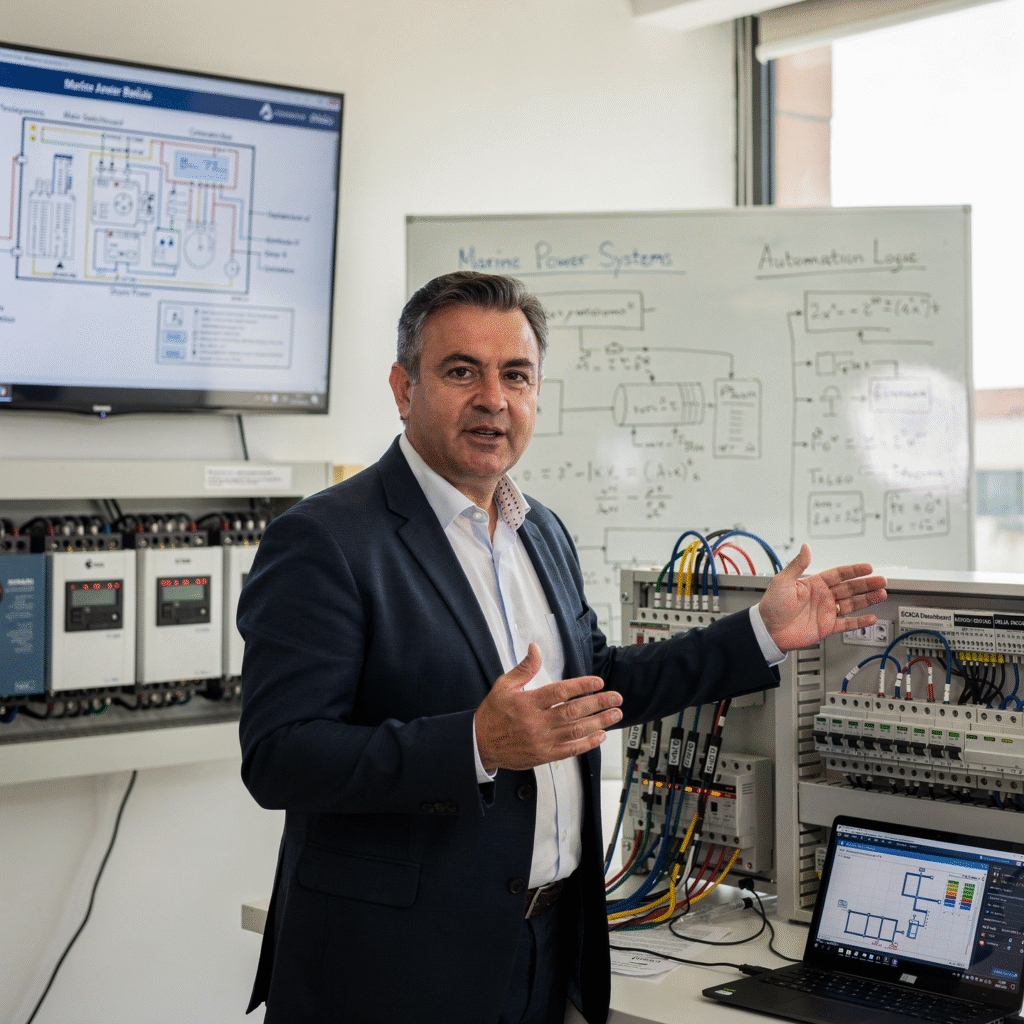
Eng. Javier Bañuls
Full Professor
Eng. Javier Bañuls
Full Professor

Dr. Nuria Llobregat
Full Professor
Dr. Nuria Llobregat
Full Professor

Dr. Pau Ferrer
Full Professor
Dr. Pau Ferrer
Full Professor

Cap. Javier Abaroa (MCA)
Full Professor
Cap. Javier Abaroa (MCA)
Full Professor
