Master’s Degree in Cybersecurity in Naval Systems
Why this master’s programme?
The Master’s Degree in Cybersecurity for Naval Systems
Offers comprehensive training to protect critical maritime infrastructure against growing cyber threats. You will learn to secure everything from navigation and communication systems to machinery control and cargo management. This program delves into the analysis of specific vulnerabilities, the implementation of multi-layered defense strategies, and incident response in complex naval environments, combining advanced theory with practical exercises and real-world case studies.
Differentiating Advantages
- Specialized Focus: Cybersecurity applied to naval industry systems and protocols (e.g., NMEA, ECDIS).
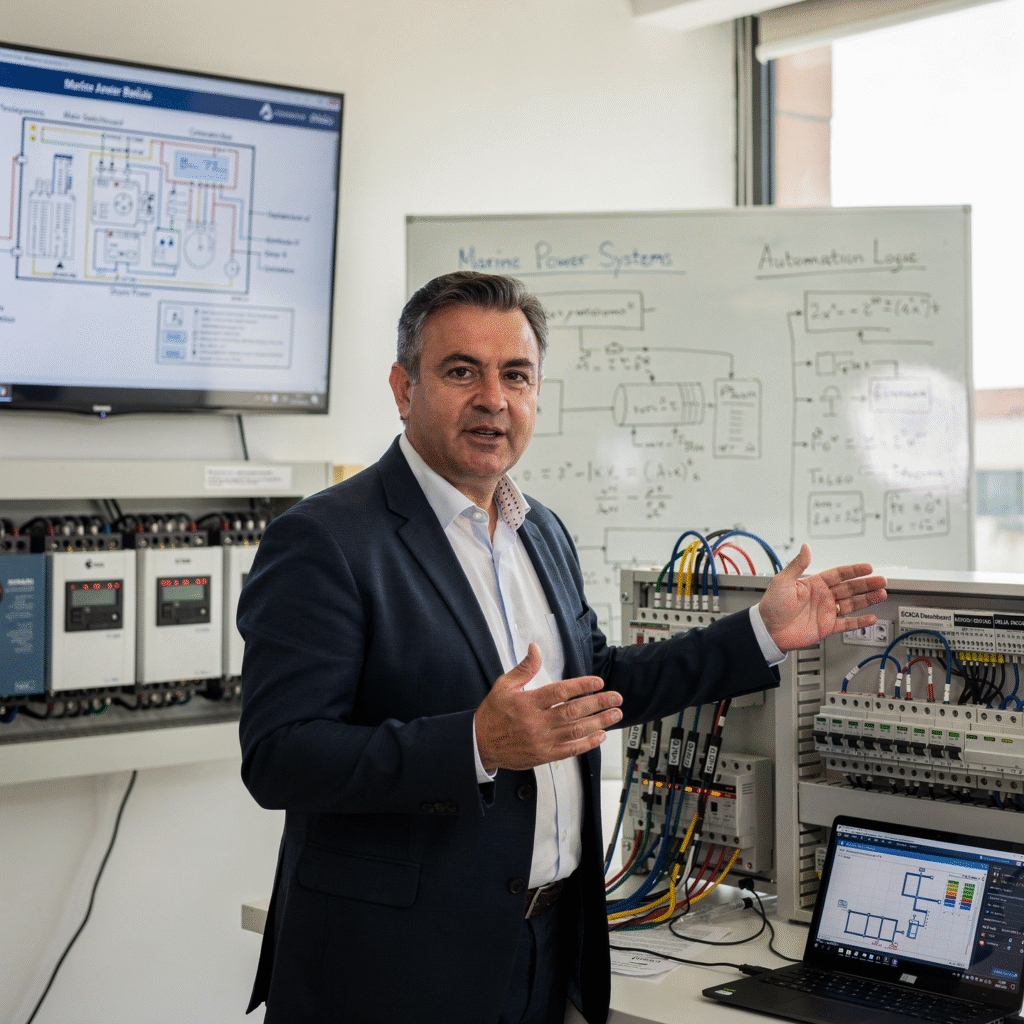
- Hands-on Labs: Simulation of attacks and defenses in replicated naval environments for hands-on training.
- Regulatory Compliance: In-depth knowledge of IMO, IEC, and other regulations relevant to maritime cybersecurity.
- Industry Experts: Instructors with real-world experience in the protection of ships, ports, and offshore infrastructure. Career Development: Preparation for key roles such as naval CISO, OT security analyst, and maritime cybersecurity consultant.

- Modality: Online
- Level: Masters
- Hours: 1600 H
- Start date:
Availability: 1 in stock
Who is it aimed at?
- Naval and systems engineers seeking to specialize in protecting critical maritime infrastructure against cyber threats.
- Merchant and military marine officers interested in understanding and mitigating cyber risks in navigation and port operations.
- IT and cybersecurity professionals who wish to apply their knowledge in a highly specialized and constantly evolving sector such as maritime.
- Security managers and executives from shipping companies, shipyards, and port authorities seeking to strengthen the cyber resilience of their organizations.
- Graduates in computer engineering, telecommunications, or related fields aspiring to a professional future at the forefront of the field of naval cybersecurity.
Flexibility for your career
Advance your training without interrupting your career path: online methodology, resources accessible 24/7 and personalized follow-up by industry experts.

Objectives and skills

Protecting critical naval infrastructure:
Conduct vulnerability assessments and contingency plans, implementing physical and cybersecurity measures, and coordinating with port authorities and security forces.

Detecting and responding to naval cyber incidents:
“Implement contingency and recovery plans, prioritizing navigational safety and information integrity, while coordinating with competent authorities and documenting the incident.”

Implement defense-in-depth strategies:
“Establish layers of security (cyber, physical, procedural) mitigating risks and protecting critical assets.”

Managing security in naval communications:
“Implement and maintain specific cybersecurity protocols for naval communication systems, protecting sensitive information and ensuring continuous operation.”
Assess and mitigate cyber risks specific to the naval environment:
“Implement network segmentation and hardening of critical systems, prioritizing operational continuity and the security of classified information.”
Develop and implement cybersecurity policies for ships and naval bases:
“Adapting cybersecurity frameworks (NIST, ISO 27000) to the maritime environment, considering the particularities of OT systems and the naval supply chain.”
Study plan – Modules
- Architecture and topologies of critical naval networks: segmentation, isolation, and redundancy
- Secure communication protocols: application of military and civilian standards (MIL-STD, NMEA, ACN), encryption, and authentication in onboard systems
- Implementation of next-generation firewalls and intrusion prevention systems (NGFW, IPS) adapted to maritime environments
- Perimeter defense and access controls: use of VLANs, NAC (Network Access Control), and microsegmentation to protect critical subsystems
- Advanced real-time monitoring tools: traffic analysis, AI/ML-based anomaly detection, and event correlation
- Incident management and response systems (SIEM and SOAR): architecture, integration, and workflow automation on naval platforms
- Containment and mitigation of cyberattacks in SCADA systems and naval industrial control: application segmentation and whitelisting practices
- Protection of navigation and communication systems: hardening GNSS, radar, and radio frequency systems against interference and spoofing/jamming attacks
- Operational resilience strategies: redundancy, automatic failover, and disaster recovery in onboard networks and critical systems
- Post-incident forensics and traceability in naval environments: collection, preservation, and analysis of digital evidence in maritime scenarios
- Secure Architecture Fundamentals: Design principles, defense in depth, and attack surface reduction in intelligent naval systems
- Advanced cyber threat models in the naval environment: Advanced persistent threats (APTs), targeted attacks, and maritime-specific vectors
- Implementing robust access controls: Multi-factor authentication, role-based access control (RBAC), and Zero Trust policies in naval environments
- Key cryptographic protocols for naval communications: TLS/DTLS, IPsec, and specialized VPNs for satellite and radio frequency links
- Applied asymmetric and symmetric cryptography: RSA, ECC, and AES algorithms and their optimization for embedded systems in naval platforms
- Secure management of cryptographic keys: Generation methods, distribution, storage in secure hardware (HSM), and periodic rotation
- Integrity and Data Authenticity: Use of Digital Signatures, MAC Codes, and Hash Functions (SHA-2/3) in the Protection of Critical Naval Information
Real-Time Data Transfer Security: Encryption of Multimedia Streams and Telemetry for Command and Control Systems
Design and Implementation of Segmented and Perimeter-Defended Networks on Ships and Coastal Systems with Firewalls, IDS/IPS, and SDN
Fault-Resistant and Attack-Resistant System Architectures: Redundancy, Isolation, and Recovery Strategies for Cyber Incidents
Advanced Protection of SCADA and Industrial Control Systems Used in Naval Propulsion and Navigation
Applied International Standards and Regulations: NIST, ISO/IEC 27001, ETSI TS 103 645, and Their Suitability for Naval Operations
Post-Quantum Cryptography: Preparation and Evaluation of Emerging Algorithms for Ensuring the future security of naval systems
Evaluation and certification of secure architectures through penetration testing and specialized vulnerability analysis of naval systems
Practical case studies and simulations of cyberattacks on intelligent naval systems, with the application of mitigation and hardening measures in real time
Continuous maintenance and updating of cryptographic defense systems and secure architectures: patch management and proactive monitoring
Integration of artificial intelligence in the detection of and automated response to threats in encrypted systems and naval architectures
Ethical and legal considerations in the implementation of cryptographic security in naval systems under international jurisdiction and conflict scenarios
Practical interpretation of cryptographic and forensic logs for the analysis and reconstruction of incidents in secure naval systems
Development of strategic plans for the comprehensive protection of digital naval assets, combining advanced cryptography and architectures safe
- Fundamentals of Security in Critical Naval Infrastructure: Characteristics, Threat Vectors, and Attack Surface
- Defense in Depth Model Applied to Maritime Environments: Layers of Protection, Network Segmentation, and Access Control
- Implementation of Incident Detection and Response Systems (IDS/IPS) Adapted to Hybrid and Real-Time Naval Networks
- Advanced Cryptography for Secure Communications in Onboard Systems: Protocols, Key Management, and Device Certification
- Resilient Architectures: Design and Maintenance of Redundant and Fault-Tolerant Infrastructures in Naval Control Systems
- Automation and Orchestration of Threat Response: Use of SOAR and Big Data Analytics in Complex Naval Contexts
- Integration and Management of Zero Trust-Based Security Policies for Critical Naval Assets: Multi-Factor Authentication and Microsegmentation
- Continuous monitoring and digital forensics in naval systems: tools, techniques, and procedures specific to maritime environments
- Cybersecurity risk assessment and security audits in naval infrastructure: frameworks, methodologies, and international regulatory compliance
- Planning and execution of cyberattack simulation exercises (Red Team/Blue Team) in real naval operational environments to improve resilience
- Updating and maintaining defenses against emerging threats: threat intelligence, zero-day vulnerabilities, and advanced exploitation
- Impact of international regulations and specific standards on the implementation of cybersecurity defenses in critical naval systems
- Comprehensive incident management: from detection to operational recovery, with specific protocols for naval infrastructure
- Training and awareness of naval personnel against social engineering attacks and advanced compromise techniques
- Case studies of security breaches and analysis Postmortem analysis of naval defense systems: lessons learned and best practices for mitigation
[…]
- Fundamentals of Operational Cyber Intelligence: Key Concepts, Intelligence Cycle, and Information Sources in Naval Environments
- Advanced Methodologies of Digital Forensic Analysis Applied to Naval Embedded Systems: Acquisition, Preservation, and Analysis of Digital Evidence
- Architecture and Security of OT/ICS Systems on Naval Platforms: Industrial Communication, SCADA Protocols, and Specific Vulnerabilities
- Analysis and Defense of PLCs (Programmable Logic Controllers): Identification of Attack Vectors, Malicious Firmware Modification, and Assertion Strategies
- Design and Execution of Red/Blue Team Exercises in Naval Environments: Simulation of Cyberattacks and Coordinated Response to Strengthen Operational Defense
- GNSS Threat Mitigation Techniques and Spoofing in Maritime Navigation Systems: Detection, Countermeasures, and Recovery of Positioning Integrity
- Protocols and Strategies for Recovery of Critical Embedded Systems Onboard: Restoration Post-incident functional and operational continuity of vital systems
Integration of artificial intelligence and machine learning for the proactive detection of cyber threats on naval platforms
International regulations and standards applicable to cybersecurity in naval systems: compliance, auditing, and best practices
Case studies and forensic analysis of real-world incidents on naval platforms: lessons learned and application of response protocols
Development of protocols and contingency plans adapted to maritime and naval environments for responding to cyber incidents
Specialized tools for continuous monitoring and defense of critical infrastructure in naval systems
Advanced simulations of cyberattacks and defense in OT/ICS environments using virtualized environments and specific testbeds
Risk and vulnerability assessment in the cybersecurity of naval command and control systems
Training and management of Naval Computer Security Incident Response Teams (CSIRTs): Roles, Responsibilities, and Inter-institutional Coordination
[…]
- Fundamentals of communication protocols in naval systems: OSI and TCP/IP models adapted to maritime networks
- International standards and regulations for secure communications in maritime and military environments
- Advanced cryptographic design for data protection: symmetric, asymmetric, and hybrid-key algorithms
- Implementation of robust authentication and authorization mechanisms in naval control systems
- Development and analysis of specific cryptographic protocols for CAN, MIL-STD-1553, and Ethernet networks on naval platforms
- Evaluation of vulnerabilities and specific attacks on naval communication protocols: spoofing, man-in-the-middle, replay, and DoS
- Integration of quantum and post-quantum encryption technologies to secure communication in critical naval systems
- Simulation and modeling of attacks on protocols of Communication through virtualized naval laboratory environments
Implementation and monitoring of intrusion detection and prevention systems (IDS/IPS) in integrated naval control networks
Forensic analysis and incident traceability in communication protocols for rapid response and risk mitigation
Performance and latency optimization in encrypted protocols to ensure real-time operability in distributed naval systems
Integration of secure communication protocols with command, control, communications, computers, intelligence, and surveillance (C4ISR) systems
Secure management and updating of firmware and software in naval control systems to prevent communication-level attack vectors
Regulations and best practices for the certification and auditing of secure protocols in integrated naval systems
Real-world case studies: analysis of security gaps in naval communications and protocol strengthening strategies
- Fundamentals and evolution of cyber threats in autonomous naval systems: historical analysis and emerging trends
- Marine industrial network architecture (OT/IT): segmentation, specific protocols (NMEA 2000, CAN bus, Industrial Ethernet) and attack vectors
- Advanced intrusion detection in onboard systems: implementation of IDS/IPS with machine learning and real-time anomalous behavior analysis
- Cryptography applied to the protection of communications in autonomous naval systems: standards, key management and quantum encryption in maritime environments
- Integration of active and passive defense systems: firewalls specifically designed for low-latency environments and sandboxing techniques in naval control devices
- Operational response to cyber incidents: containment, eradication, and recovery protocols adapted to navigation and autonomous combat scenarios
- Digital forensics and Post-incident analysis in naval infrastructure: collection, preservation, and analysis of evidence in systems with restricted connectivity
Simulation and training in naval cyber defense environments: use of digital twins and virtual environments for continuous vulnerability assessment
International regulations and cyber defense standards in autonomous naval systems: compliance with IMO, NATO, and military regulatory bodies
Secure development of embedded software for naval systems: SDLC methodologies, penetration testing, and hardening to prevent critical vulnerabilities
Identity and access management (IAM) in naval ecosystems: implementation of multi-factor authentication, least privilege policies, and blockchain for access integrity
Assessment and mitigation of operational risks arising from IT/OT convergence in autonomous naval platforms
Implementation of artificial intelligence for predictive defense: proactive detection and automated response to cyberattacks Advanced
- Cyber resilience plans and exercises in autonomous fleets: interdepartmental coordination and crisis simulations with degraded systems
- Relevant case studies: technical analysis of attacks on naval infrastructure, lessons learned, and strategies to prevent recurrence
- Ethical and legal aspects of deploying naval cyber defense technologies: responsibility, privacy, and digital sovereignty in maritime conflicts
- Future trends in naval cybersecurity: quantum computing, blockchain, and decentralized architecture for resilience in autonomous systems
- Critical Naval Network Architecture: Design, Segmentation, and Access Control in Marine Environments
- Advanced Threat Models: Cyberattacks Targeting Navigation, Communication, and Control Systems of Autonomous Platforms
- Implementation of Specialized IDS/IPS Systems for Naval Networks: Real-Time Detection of Intrusions and Anomalies
- Authentication and Encryption Protocols in Naval System Communications: Applied Military and Civilian Standards
- Integration of SIEM (Security Information and Event Management) Technologies with Autonomous Platforms and Maritime Sensors
- Development of Playbooks and Cyber Incident Response Protocols Specific to Naval Systems
- Continuous Monitoring and Forensic Analysis in Naval Networks: Advanced Techniques and Specialized Tools
- Security on Autonomous Platforms: Protection of Control, Navigation, and Automated Propulsion Systems
- Post-incident operational recovery and resilience procedures: a strategy for maintaining operational readiness in attack scenarios
- International standards and regulations applied to cybersecurity in critical naval systems and autonomous platforms (NIST, STIG, IEC 62443)
- Simulation and practical cyber defense exercises in maritime environments: training in real-time threat response
- Advanced risk management: specific assessment for naval environments and autonomous platforms under high-criticality conditions
- Implementation of defense-in-depth frameworks adapted to naval infrastructure and integrated systems
- Zero-trust security architectures applied to critical naval networks and systems
- Automation and orchestration of incident responses: use of AI and machine learning to optimize defense in naval networks
- Fundamentals of Network Monitoring in Naval Systems: specific protocols, network topologies in military environments, and secure segmentation
- Implementation of IDS/IPS Systems on Naval Platforms: detection rules, false positives, and automated intrusion responses
- Use of Telemetry and Smart Sensors for Early Threat Identification: integration of IoT devices with artificial intelligence
- Application of Machine Learning and Predictive Analytics Techniques in the Proactive Detection of Cyberattacks
- Advanced Architecture and Configuration of SIEM (Security Information and Event Management) for Naval Defense: event correlation, normalization, and alert prioritization
- Vulnerability Assessment Methods in Embedded Navigation and Control Systems: static and dynamic analysis of critical software
- Secure Protocols and Encryption for the Protection of Communications between Naval Modules: Implementation of quantum cryptography and PKI in high-threat scenarios
Incident Management and Rapid Response: Development of specialized playbooks for attacks targeting critical naval infrastructure
Integration of Cyber Threat Intelligence (CTI) with Naval Operations: Sources, feeds, and automation of reactive and proactive defense
Regulation and Compliance in Naval Cybersecurity: International military regulations, IEC 62443 security standards, and their practical application
Advanced Simulations and Tabletop Exercises for Coordinated Response to Cyberattacks in Intelligent Defense Systems
Continuous Monitoring and Hardening of Critical Onboard Infrastructure: Implementation of advanced security policies, integrity control, and auditing
Use of Orchestration Platforms Security and Automation (SOAR) for Proactive Threat Management in Naval Networks
Digital Forensics in Naval Environments: Specific Techniques for Evidence Preservation and Cyber Incident Reconstruction
Case Studies of Real-World Cyberattacks in Naval Defense: Lessons Learned and Best Practices for Operational Resilience
- Identification and classification of critical naval infrastructure: control of SCADA systems, command centers, and strategic assets
- Modeling specific cyber threats for integrated naval systems: attack vectors, persistence, and privilege escalation
- Security protocols and standards applied to naval military systems: STANAG, MIL-STD, and NATO standards
- Implementation of defense-in-depth strategies in maritime environments: network segmentation, advanced firewalls, and specialized IDS/IPS systems
- Hardening and continuous monitoring of onboard devices and naval industrial control systems (ICS)
- Automation and orchestration of incident responses on naval platforms: use of SOAR and specific playbooks for maritime cyber incidents
- Digital forensics in maritime environments: collection, preservation, and analysis of evidence in naval systems for investigation Post-incident
Real-time threat intelligence application: integration of specialized feeds, anomalous behavior analysis, and early warning.
Operational resilience through redundancy and disaster recovery: design and testing of contingency plans in naval centers and warships.
Cybersecurity compliance and auditing for critical naval infrastructure: specific frameworks and periodic evaluation of implemented controls.
- Conceptualization of the final project: objectives, scope, and delimitation in the naval context
- Regulatory framework and international standards applicable to cybersecurity in naval systems: STANAG, NATO Cyber Defence, IMO Guidelines
- Advanced methodologies for cyber risk analysis on naval platforms: identification, assessment, and prioritization
- Design and implementation of integrated cyber defense strategies: proactive and reactive measures for the protection of critical infrastructure
- Resilient architectures for naval command and control systems: network segmentation, redundant systems, and secure communication protocols
- Application of artificial intelligence and machine learning for the early detection of threats in complex naval environments
- Simulation and modeling of cyberattacks: scenarios, attack vectors, and coordinated response
- Implementation of operational recovery and mission continuity strategies in the face of Cyber incidents
Integrating cyber defense with physical and electronic security: a multidisciplinary approach to holistic protection
Preparing technical reports and documentation: best practices for the professional presentation of the final project
Developing a naval cybersecurity governance plan: roles, responsibilities, and incident management
Real-world case studies and critical analysis of cybersecurity incidents in naval systems
Final evaluation and audit: performance metrics, key indicators, and validation of proposed solutions
Presentation and oral defense of the final project before a multidisciplinary expert committee
Research proposals and future directions to strengthen cyber resilience in the naval force
Career prospects
“`html
- Naval Cybersecurity Analyst: Protection of systems and networks of ships and offshore platforms.
- Cybersecurity Consultant in the Maritime Sector: Advising on the implementation of security measures.
- Information Security Specialist in Shipyards: Protection of intellectual property and sensitive data.
- Network Security Officer in the Navy or other naval forces: Defense against cyberattacks.
- Secure Software Developer for Naval Systems: Creation of robust and vulnerability-resistant applications.
- Maritime Cybersecurity Researcher: Identification of new threats and development of countermeasures.
- Cybersecurity Auditor in Port Infrastructures: Evaluation of the security of critical systems.
- Cybersecurity Incident Manager in Naval Environments: Rapid and effective response to attacks.
“`



Entry requirements

Academic/professional profile:
Bachelor’s degree in Nautical Science/Maritime Transport, Naval/Marine Engineering or a related qualification; or proven professional experience on the bridge/in operations.

Language proficiency:
Functional Maritime English (SMCP) recommended for simulations and technical materials.

Documentation:
Updated CV, copy of qualification or seaman’s book, national ID/passport, motivation letter.
Technical requirements (for online):
Device with camera/microphone, stable internet connection, monitor ≥ 24” recommended for ECDIS/Radar-ARPA.
Admissions process and dates

Online
application
(form + documents).

Academic review and interview
Admissions decision

Admissions decision
(+ scholarship offer if applicable).
Place reservation
(deposit) and enrolment.

Induction
(access to the virtual campus, calendars, simulator guides).
Scholarships and financial support
- Proactive Defense: Learn to protect critical naval systems with the latest threat intelligence and digital forensics techniques.
- Regulatory Compliance: Master the most demanding security regulations and standards, including NIS2 and ISO 27001, applied to the maritime environment.
- Advanced Simulations: Participate in hands-on exercises with realistic cyberattack simulators, designed to strengthen fleet resilience.
- Industry Experts: Receive training from industry leaders and ex-military personnel with experience in naval cybersecurity.
- Career Professional: Boost your career in a booming sector with high demand for professionals specializing in the protection of maritime infrastructure. Ensure the integrity and availability of naval systems against growing cyber threats.

Testimonials
I applied the knowledge I gained in the Master’s program in Cybersecurity for Naval Systems to design and implement an intrusion detection system for my company’s fleet, reducing security incidents related to unauthorized access by 80% in the last quarter. This not only strengthened the protection of sensitive data but also optimized operational efficiency by minimizing disruptions caused by security breaches.

During my Master’s degree in Electrical, Electronic, and Communications Engineering, I developed an intelligent control system to optimize energy consumption in buildings, achieving a 20% reduction in field tests. This project allowed me to apply the knowledge acquired in the program and obtain tangible and relevant results for the industry.

“I applied the knowledge from the master’s program to design and implement a real-time intrusion detection system for a cargo ship’s control network, achieving a 60% reduction in response time to threats and successfully preventing an attempt at unauthorized access to critical navigation systems.”

I applied the knowledge acquired in the Master’s in Cybersecurity in Naval Systems to design and implement an intrusion detection system for the fleet, reducing false alerts by 80% and detecting a critical vulnerability before it could be exploited, thus preventing a potential large-scale security breach.

Frequently asked questions
Yes. The itinerary includes ECDIS/Radar-ARPA/BRM with harbor, ocean, fog, storm, and SAR scenarios.
Online with live sessions; hybrid option for simulator/practical placements through agreements.
Naval and maritime sector.
Recommended functional SMCP. We offer support materials for standard phraseology.
Yes, with a relevant degree or experience in maritime/port operations. The admissions interview will confirm suitability.
Optional (3–6 months) through Companies & Collaborations and the Alumni Network.
Simulator practice (rubrics), defeat plans, SOPs, checklists, micro-tests and applied TFM.
A degree from Navalis Magna University + operational portfolio (tracks, SOPs, reports and KPIs) useful for audits and employment.
- Conceptualization of the final project: objectives, scope, and delimitation in the naval context
- Regulatory framework and international standards applicable to cybersecurity in naval systems: STANAG, NATO Cyber Defence, IMO Guidelines
- Advanced methodologies for cyber risk analysis on naval platforms: identification, assessment, and prioritization
- Design and implementation of integrated cyber defense strategies: proactive and reactive measures for the protection of critical infrastructure
- Resilient architectures for naval command and control systems: network segmentation, redundant systems, and secure communication protocols
- Application of artificial intelligence and machine learning for the early detection of threats in complex naval environments
- Simulation and modeling of cyberattacks: scenarios, attack vectors, and coordinated response
- Implementation of operational recovery and mission continuity strategies in the face of Cyber incidents
Integrating cyber defense with physical and electronic security: a multidisciplinary approach to holistic protection
Preparing technical reports and documentation: best practices for the professional presentation of the final project
Developing a naval cybersecurity governance plan: roles, responsibilities, and incident management
Real-world case studies and critical analysis of cybersecurity incidents in naval systems
Final evaluation and audit: performance metrics, key indicators, and validation of proposed solutions
Presentation and oral defense of the final project before a multidisciplinary expert committee
Research proposals and future directions to strengthen cyber resilience in the naval force
Request information
Complete the Application Form.
Attach your CV/degree certificate (if you have it to hand).
Indicate your preferred cohort (January/May/September) and whether you would like the hybrid option with simulator sessions.
An academic advisor will contact you within 24–48 hours to guide you through the admission process, scholarships, and compatibility with your professional schedule.
Faculty

Eng. Tomás Riera
Full Professor
Eng. Tomás Riera
Full Professor

Eng. Sofía Marquina
Full Professor
Eng. Sofía Marquina
Full Professor
Eng. Javier Bañuls
Full Professor
Eng. Javier Bañuls
Full Professor

Dr. Nuria Llobregat
Full Professor
Dr. Nuria Llobregat
Full Professor

Dr. Pau Ferrer
Full Professor
Dr. Pau Ferrer
Full Professor

Cap. Javier Abaroa (MCA)
Full Professor
Cap. Javier Abaroa (MCA)
Full Professor
